ONS Migration of Monolith to Microservices
Some of the highlights from this project that were built by Noisy Atom
- Deployed initial python Flask components on the first sprints for ONS Show and Tell
- Instigated BDD testing component for the first beta microservice using python Bamboo
- Forked and enhanced the ONS OAuth2 server taken from Richard Knopps OS Django OAuth2 server
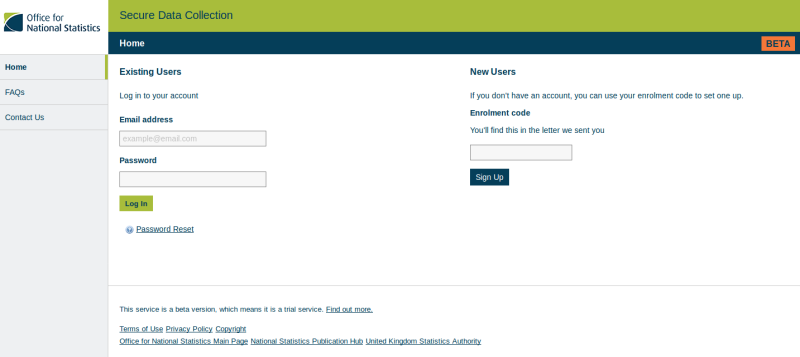
OAuth2 Using Django Webserver
The system had a front end UI written in Flask. Noisy Atom and one other contractor provided the first beta version of this application. The microservice had a requirement to use OAuth2 as it's token based authentication framework.
Noisy Atom took an outstanding Django implementation of this and adapted for ONS. It predominantly used a legacy flow for one microservice gaining access to another on behalf of a user. In our case the Django servers was a headless service exposing a REST interface.
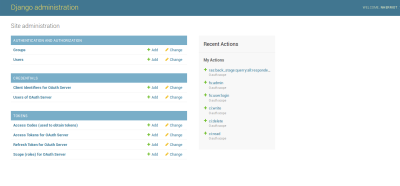
Administration Of OAuth2
ONS required that users could be added and removed to the OAuh2 server. This was not part of OAuth2 specifications and is something typically provided by 3rd party plugins or software. Noisy Atom provided a REST endpoint allowing a microservice to control the adding and removing of users.
This takes 'eating your own dog food' to a new level. As the administration system itself had to be a granted and added to the OAuth2 server - thus using 'client credentials' grant to get a token.
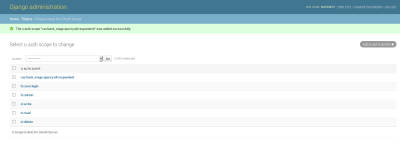
OAuth2 And Scopes
The server allowed 'scopes' to be defined and added to the system. Hence the administrator could pre-provision a scope which could allow a particular microservice access to features or data on the private network.
This allowed flexibility on how microservices communicated with each other. Further work is being done by Noisy Atom to take the Open Source project further by providing features such as:
- per user defined scopes
- encryption selection of tokens from opaque or JWT
- python 3 compatible